:: Thierry – Shading ::
Author: Dennis
Art & Images: Thierry – shading
:: Thierry – Shading ::
SURBL.ORG
Today I read in a paper about surbl.org
SURBL – Spam URI Realtime Blocklists
Together with Spamassassin and Spamcopuri I have installed now a much more improved spamfilter at my webserver. Kewl ..
After running it for a number of hours now I can only say: use it!
Art & Images: Bill
:: Bill, digital willy ::
Art & Images: Bill
:: Bill, digital willy ::
Searching with Yahoo
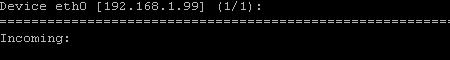
nload
Our new Home
The Ylympics
For my wife en best girlfriend; Ylympics
Tech Geek News: Bluetooth Vulnerability Widcomm Software
Yesterday I got the message (or read) that the most used software for Bluetooth Dongles, Widcomm software has a Vulnerability.
WIDCOMM Bluetooth Connectivity Software Buffer Overflows
Okay, that’s a little shocking as 70 to 80 percent of the Bluetooth Dongles sold do use this application Software.
The vendor status about this vulnerability is that Release 3.0 will fix this issue.
Little facts
Right now Widcomm is sold to many vendors using different IC’s. Among them are Ie. Broadcom and CSR (Bluecore2) with Bluetooth spec. 1.1
Versions of Widcomm are sold up to version 1.4.2.x but no updates for BT 1.1 are expected anymore.
Widcomm has been aquired by Broadcom a few month’s ago.
The Widcomm software BTW 3.0 does only work with bluetooth spec 1.2 and is only? working together with the broadcom chipset. It’s hardly to believe that the CSR chipset (Bluecore3) can operate together with this Widcomm (BTW 3.0) software
So in fact the BTW 3.0 software is not the real solution as allmost 99% of all dongles sold in the past are BT spec 1.1
Solutions are:
Using: IVT software, Using Microsoft’s SP2 with XP with standard bluetooth support (but lack of many profiles).
set the Bluetooth device configuration to be non-discoverable or hidden. This will not stop the device from being vulnerable but it may limit the exposure or stop using bluetooth ;-)
The choice is yours.